While Quick Defrag is running, it will make it so you cannot run any programs on your computer. It will block task manager and other tools too telling you that your hard drive is corrupted. The fake error message that you will see when you attempt to run a program is:
Windows detected a hard drive problem.It will also display fake notifications from your task bar.
A hard drive error occurred while starting the application.
Critical Error
Hard Drive not found. Missing hard drive.
Critical Error
RAM memory usage is critically high. RAM memory failure.
Critical ErrorAs you can see, Quick Defrag is a typical rip-off rogue application. If you have already purchased it then you should contact your credit card company and dispute the charges because QuickDefrag is a scam. Be advised, that this rogue program can come bundled with other malicious software, adware, rootkits, etc. In order to completely remove Quick Defrag from your computer, please follow the steps in the removal guide below. If you've got any further questions about this fake scanner, please leave a comment below. Good luck and be safe online!
A critical error has occurred while indexing data stored on hard drive. System restart required.
Quick Defrag removal instructions:
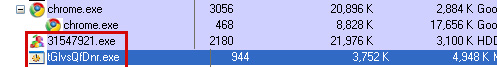
1. Open Task Manager (Ctrl+Alt+Delete) or use Process Explorer.
2. Click on the Processes tab.
3. End Quick Defrag process, e.g. tGldgRksm.exe or 1584321.exe.
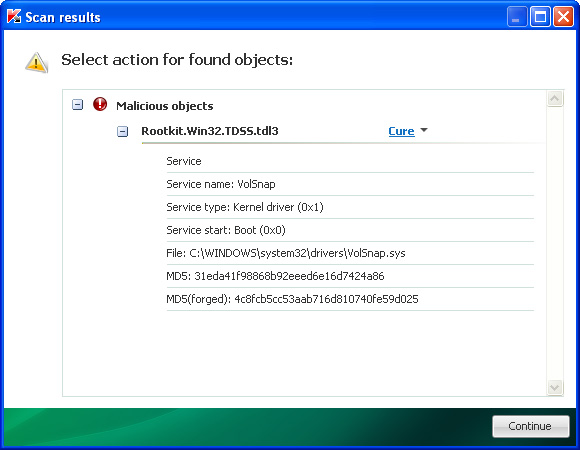
4. Download TDSSKiller (free utility from Kaspersky Lab) and run it. Remove TDSS rootkit if exist.
5. Download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to iexplore.exe or winlogon.exe With all of these tools, if running Windows 7 or Vista they MUST be run as administrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
6. New threats appear every day. In order to protect your PC from such (new) infections we strongly recommend you to use ESET Smart Security.
Quick Defrag removal instructions (in Safe Mode with Networking):
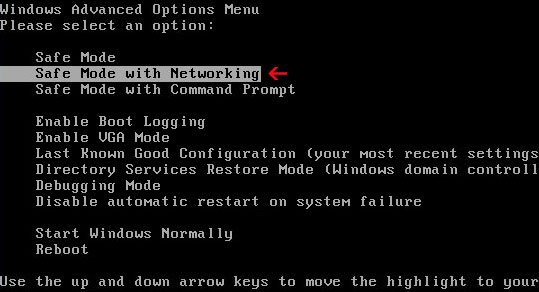
1. Reboot your computer is "Safe Mode with Networking". As the computer is booting tap the "F8 key" continuously which should bring up the "Windows Advanced Options Menu" as shown below. Use your arrow keys to move to "Safe Mode with Networking" and press Enter key. Read more detailed instructions here: http://www.computerhope.com/issues/chsafe.htm
NOTE: Login as the same user you were previously logged in with in the normal Windows mode.
2. Download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to iexplore.exe or winlogon.exe With all of these tools, if running Windows 7 or Vista they MUST be run as administrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
3. New threats appear every day. In order to protect your PC from such (new) infections we strongly recommend you to use ESET Smart Security.
Quick Defrag associated files and registry values:
Files:
- %Temp%\[SET OF RANDOM CHARACTERS].exe
- %Temp%\dfrg
- %Temp%\dfrgr
- %Temp%\[SET OF RANDOM CHARACTERS].dll
- %UserProfile%\Desktop\Quick Defrag.lnk
- %UserProfile%\Start Menu\Programs\Quick Defrag\
- %UserProfile%\Start Menu\Programs\Quick Defrag\Quick Defrag.lnk
- %UserProfile%\Start Menu\Programs\Quick Defrag\Uninstall Quick Defrag.lnk
C:\Documents and Settings\[UserName]\Local Settings\Temp (in Windows 2000/XP)
C:\Users\[UserName]\AppData\Local\Temp (in Windows Vista & Windows 7)
%UserProfile% refers to:
C:\Documents and Settings\[UserName]\ (in Windows 2000/XP)
C:\Users\[UserName]\ (in Windows Vista & Windows 7)
Registry values:
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "[SET OF RANDOM CHARACTERS]"
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "[SET OF RANDOM CHARACTERS].exe"















0 comments:
Post a Comment